CCNA 4 R&S: Connecting Networks Chapter 7 v5.02 + v5.03 Exam Answers 2016
LAST UPDATE: TODAY
1. How is “tunneling” accomplished in a VPN?
New headers from one or more VPN protocols encapsulate the original packets.*
All packets between two hosts are assigned to a single physical medium to ensure that the packets are kept private.
Packets are disguised to look like other types of traffic so that they will be ignored by potential attackers.
A dedicated circuit is established between the source and destination devices for the duration of the connection.
All packets between two hosts are assigned to a single physical medium to ensure that the packets are kept private.
Packets are disguised to look like other types of traffic so that they will be ignored by potential attackers.
A dedicated circuit is established between the source and destination devices for the duration of the connection.
2. Which two scenarios are examples of remote access VPNs? (Choose two.)
A toy manufacturer has a permanent VPN connection to one of its parts suppliers.
All users at a large branch office can access company resources through a single VPN connection.
A mobile sales agent is connecting to the company network via the Internet connection at a hotel.*
A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ.
An employee who is working from home uses VPN client software on a laptop in order to connect to the company network.*
All users at a large branch office can access company resources through a single VPN connection.
A mobile sales agent is connecting to the company network via the Internet connection at a hotel.*
A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ.
An employee who is working from home uses VPN client software on a laptop in order to connect to the company network.*
3.

Refer to the exhibit. Which IP address would be configured on the tunnel interface of the destination router?

Refer to the exhibit. Which IP address would be configured on the tunnel interface of the destination router?
172.16.1.1
172.16.1.2*
209.165.200.225
209.165.200.226
172.16.1.2*
209.165.200.225
209.165.200.226
4. Which statement correctly describes IPsec?
IPsec works at Layer 3, but can protect traffic from Layer 4 through Layer 7.*
IPsec uses algorithms that were developed specifically for that protocol.
IPsec implements its own method of authentication.
IPsec is a Cisco proprietary standard.
IPsec uses algorithms that were developed specifically for that protocol.
IPsec implements its own method of authentication.
IPsec is a Cisco proprietary standard.
5. What is an IPsec protocol that provides data confidentiality and authentication for IP packets?
AH
ESP*
RSA
IKE
ESP*
RSA
IKE
6. Which three statements describe the building blocks that make up the IPsec protocol framework? (Choose three.)
IPsec uses encryption algorithms and keys to provide secure transfer of data.*
IPsec uses Diffie-Hellman algorithms to encrypt data that is transferred through the VPN.
IPsec uses 3DES algorithms to provide the highest level of security for data that is transferred through a VPN.
IPsec uses secret key cryptography to encrypt messages that are sent through a VPN.*
IPsec uses Diffie-Hellman as a hash algorithm to ensure integrity of data that is transmitted through a VPN.
IPsec uses ESP to provide confidential transfer of data by encrypting IP packets.*
IPsec uses Diffie-Hellman algorithms to encrypt data that is transferred through the VPN.
IPsec uses 3DES algorithms to provide the highest level of security for data that is transferred through a VPN.
IPsec uses secret key cryptography to encrypt messages that are sent through a VPN.*
IPsec uses Diffie-Hellman as a hash algorithm to ensure integrity of data that is transmitted through a VPN.
IPsec uses ESP to provide confidential transfer of data by encrypting IP packets.*
7. What key question would help determine whether an organization should use an SSL VPN or an IPsec VPN for the remote access solution of the organization?
Is a Cisco router used at the destination of the remote access tunnel?
What applications or network resources do the users need for access?
Are both encryption and authentication required?
Do users need to be able to connect without requiring special VPN software?*
What applications or network resources do the users need for access?
Are both encryption and authentication required?
Do users need to be able to connect without requiring special VPN software?*
8. What is the purpose of a message hash in a VPN connection?
It ensures that the data cannot be duplicated and replayed to the destination.
It ensures that the data is coming from the correct source.
It ensures that the data has not changed while in transit.*
It ensures that the data cannot be read in plain text.
It ensures that the data is coming from the correct source.
It ensures that the data has not changed while in transit.*
It ensures that the data cannot be read in plain text.
9. A network design engineer is planning the implementation of a cost-effective method to interconnect multiple networks securely over the Internet. Which type of technology is required?
a dedicated ISP
a VPN gateway*
a leased line
a GRE IP tunnel
a VPN gateway*
a leased line
a GRE IP tunnel
10. What is one benefit of using VPNs for remote access?
lower protocol overhead
potential for reduced connectivity costs *
increased quality of service
ease of troubleshooting
potential for reduced connectivity costs *
increased quality of service
ease of troubleshooting
11. Which statement describes a characteristic of IPsec VPNs?
IPsec can secure traffic at Layers 1 through 3.
IPsec works with all Layer 2 protocols.*
IPsec encryption causes problems with routing.
IPsec is a framework of Cisco proprietary protocols
IPsec works with all Layer 2 protocols.*
IPsec encryption causes problems with routing.
IPsec is a framework of Cisco proprietary protocols
12. What is the purpose of the generic routing encapsulation tunneling protocol?
to support basic unencrypted IP tunneling using multivendor routers between remote sites
to provide fixed flow-control mechanisms with IP tunneling between remote sites
to manage the transportation of IP multicast and multiprotocol traffic between remote sites*
to provide packet level encryption of IP traffic between remote sites
to provide fixed flow-control mechanisms with IP tunneling between remote sites
to manage the transportation of IP multicast and multiprotocol traffic between remote sites*
to provide packet level encryption of IP traffic between remote sites
13. Which algorithm is an asymmetrical key cryptosystem?
3DES
DES
AES
RSA*
DES
AES
RSA*
14. A network design engineer is planning the implementation of an IPsec VPN. Which hashing algorithm would provide the strongest level of message integrity?
512-bit SHA*
AES
SHA-1
MD5
AES
SHA-1
MD5
15. What two encryption algorithms are used in IPsec VPNs? (Choose two.)
IKE
DH
PSK
3DES*
AES*
DH
PSK
3DES*
AES*
16. Which statement describes a feature of site-to-site VPNs?
Internal hosts send normal, unencapsulated packets.*
VPN client software is installed on each host.
The VPN connection is not statically defined.
Individual hosts can enable and disable the VPN connection.
VPN client software is installed on each host.
The VPN connection is not statically defined.
Individual hosts can enable and disable the VPN connection.
17. Which Cisco VPN solution provides limited access to internal network resources by utilizing a Cisco ASA and provides browser-based access only?
clientless SSL VPN*
IPsec
SSL
client-based SSL VPN
IPsec
SSL
client-based SSL VPN
18. Which two algorithms use Hash-based Message Authentication Code for message authentication? (Choose two.)
AES
DES
3DES
MD5*
SHA*
DES
3DES
MD5*
SHA*
19. Which function of IPsec security services allows the receiver to verify that the data was transmitted without being changed or altered in any way?
confidentiality
anti-replay protection
data integrity*
authentication
anti-replay protection
data integrity*
authentication
20.
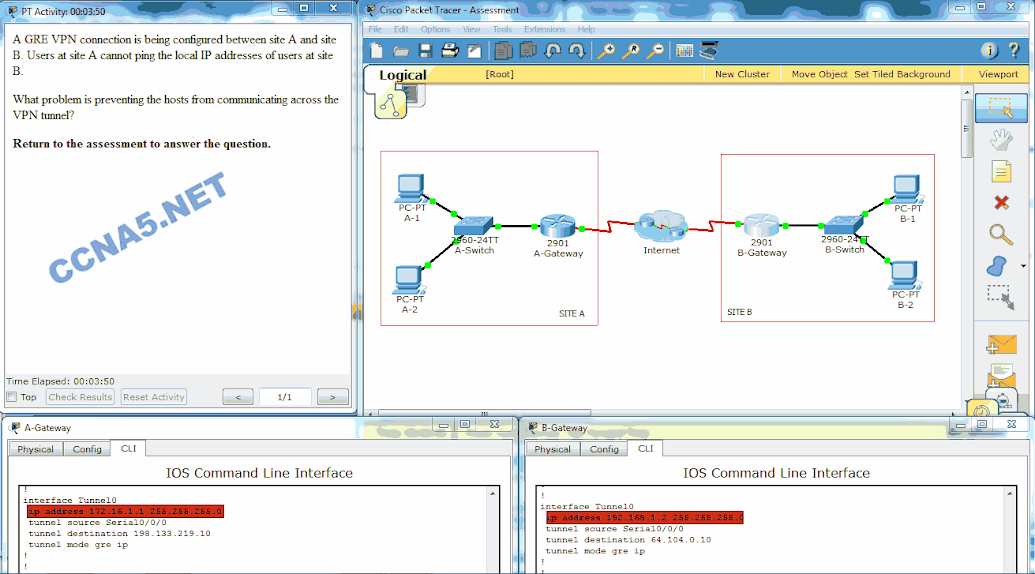
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. What problem is preventing the hosts from communicating across the VPN tunnel?
The EIGRP configuration is incorrect.
The tunnel destinations addresses are incorrect.
The tunnel IP addresses are incorrect.*
The tunnel source interfaces are incorrect
The tunnel destinations addresses are incorrect.
The tunnel IP addresses are incorrect.*
The tunnel source interfaces are incorrect
21. What is the purpose of utilizing Diffie-Hellman (DH) algorithms as part of the IPsec standard?
DH algorithms allow unlimited parties to establish a shared public key that is used by encryption and hash algorithms.
DH algorithms allow two parties to establish a shared public key that is used by encryption and hash algorithms.
DH algorithms allow two parties to establish a shared secret key that is used by encryption and hash algorithms.*
DH algorithms allow unlimited parties to establish a shared secret key that is used by encryption and hash algorithms.
DH algorithms allow two parties to establish a shared public key that is used by encryption and hash algorithms.
DH algorithms allow two parties to establish a shared secret key that is used by encryption and hash algorithms.*
DH algorithms allow unlimited parties to establish a shared secret key that is used by encryption and hash algorithms.
22.

Refer to the exhibit. A tunnel was implemented between routers R1 and R2. Which two conclusions can be drawn from the R1 command output? (Choose two.)
The data that is sent across this tunnel is not secure.*
This tunnel mode provides encryption.
This tunnel mode does not support IP multicast tunneling.
A GRE tunnel is being used.*
This tunnel mode is not the default tunnel interface mode for Cisco IOS software.
This tunnel mode provides encryption.
This tunnel mode does not support IP multicast tunneling.
A GRE tunnel is being used.*
This tunnel mode is not the default tunnel interface mode for Cisco IOS software.
23. Two corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks?
Cisco AnyConnect Secure Mobility Client with SSL
Frame Relay
remote access VPN using IPsec
Cisco Secure Mobility Clientless SSL VPN
site-to-site VPN*
Frame Relay
remote access VPN using IPsec
Cisco Secure Mobility Clientless SSL VPN
site-to-site VPN*
24. Which remote access implementation scenario will support the use of generic routing encapsulation tunneling?
a mobile user who connects to a SOHO site
a central site that connects to a SOHO site without encryption*
a branch office that connects securely to a central site
a mobile user who connects to a router at a central site
a central site that connects to a SOHO site without encryption*
a branch office that connects securely to a central site
a mobile user who connects to a router at a central site
NEW QUESTIONS
25. Which critical function that is provided by IPsec ensures that data has not been changed in transit between the source and destination?
integrity*
anti-replay protection
confidentiality
authentication
anti-replay protection
confidentiality
authentication
26. Which service of IPsec verifies that secure connections are formed with the intended sources of data?
encryption
authentication*
confidentiality
data integrity
27. Fill in the blank.
“__GRE__” is a site-to-site tunnel protocol developed by Cisco to allow multiprotocol and IP multicast traffic between two or more sites.
authentication*
confidentiality
data integrity
27. Fill in the blank.
“__GRE__” is a site-to-site tunnel protocol developed by Cisco to allow multiprotocol and IP multicast traffic between two or more sites.
28. What is an advantage of using the Cisco Secure Mobility Clientless SSL VPN?
Security is provided by prohibiting network access through a browser.
Any device can connect to the network without authentication.
Clients do not require special software.*
Clients use SSH to access network resources.
Any device can connect to the network without authentication.
Clients do not require special software.*
Clients use SSH to access network resources.
29. How can the use of VPNs in the workplace contribute to lower operating costs?
VPNs prevents connectivity to SOHO users.
VPNs can be used across broadband connections rather than dedicated WAN links.*
VPNs require a subscription from a specific Internet service provider that specializes in secure connections.
High-speed broadband technology can be replaced with leased lines.
VPNs can be used across broadband connections rather than dedicated WAN links.*
VPNs require a subscription from a specific Internet service provider that specializes in secure connections.
High-speed broadband technology can be replaced with leased lines.
30. Which two characteristics describe IPsec VPNs? (Choose two.)
Key lengths range from 40 bits to 256 bits.
IPsec authentication is one-way or two-way.
Specific PC client configuration is required to connect to the VPN.*
IPsec is specifically designed for web-enabled applications.
IPsec authenticates by using shared secrets or digital certificates.*
IPsec authentication is one-way or two-way.
Specific PC client configuration is required to connect to the VPN.*
IPsec is specifically designed for web-enabled applications.
IPsec authenticates by using shared secrets or digital certificates.*
I believe there are many more pleasurable opportunities ahead for individuals that looked at your site.Block Chain Training in Bangalore
ReplyDeleteInspiring writings and I greatly admired what you have to say , I hope you continue to provide new ideas for us all and greetings success always for you..Keep update more information..
ReplyDeleterpa training in Chennai | best rpa training in chennai
rpa training in pune
rpa online training | rpa training in bangalore
I recently came across your blog and have been reading along. I thought I would leave my first comment.
ReplyDeleteData Science training in Chennai | Data science training in bangalore
Data science training in pune| Data science online training
Python training in Kalyan nagar
I love the blog. Great post. It is very true, people must learn how to learn before they can learn. lol i know it sounds funny but its very true. . .
ReplyDeletejava training in chennai | java training in bangalore
java training in tambaram | java training in velachery
Useful information.I am actual blessed to read this article.thanks for giving us this advantageous information.I acknowledge this post.and I would like bookmark this post.Thanks
ReplyDeletePython training in marathahalli
Python training institute in pune
This comment has been removed by the author.
ReplyDeleteNice Post
ReplyDeleteFor Blockchain training in Bangalore, Visit:
Blockchain training in Bangalore
Nice blog..I searching this topic but this blog use to reading finally.. Its really wonderful thank you for your valuable sharing....
ReplyDeleteAndroid Training Institute in Chennai | Certification | Online Course Training | Android Training Institute in Bangalore | Certification | Online Course Training | Android Training Institute in Hyderabad | Certification | Online Course Training | Android Training Institute in Coimbatore | Certification | Online Course Training | Android Training Institute in Online | Certification | Online Course Training
I have read your blog its very attractive and impressive. Nice information. It helped me alot.
ReplyDeletesap training in chennai
sap training in tambaram
azure training in chennai
azure training in tambaram
cyber security course in chennai
cyber security course in tambaram
ethical hacking course in chennai
ethical hacking course in tambaram
Thank you for sharing nice blog. I hope people are getting really good information from this blog
ReplyDeleteweb designing training in chennai
web designing training in annanagar
digital marketing training in chennai
digital marketing training in annanagar
rpa training in chennai
rpa training in annanagar
tally training in chennai
tally training in annanagar
Nice blog..I searching this topic but this blog use to reading finally.. Its really wonderful thank you for your valuable sharing....
ReplyDeleteweb designing training in chennai
web designing training in omr
digital marketing training in chennai
digital marketing training in omr
rpa training in chennai
rpa training in omr
tally training in chennai
tally training in omr
It is imperative that we read blog post very carefully. I am already done it and find that this post is really amazing.
ReplyDeletedata scientist training and placement in hyderabad
ReplyDeleteGreat blog found to be well written in a simple manner that everyone will understand and gain the enough knowledge from your blog
DevOps Training in Hyderabad
It's a great pleasure reading your post.Its full of information I am looking for and I love to post a comment that "The content of your post is awesome" Great work.
ReplyDeletedata scientist training in hyderabad