1
What are two benefits of extending access layer connectivity to users through a wireless medium? (Choose two.)
What are two benefits of extending access layer connectivity to users through a wireless medium? (Choose two.)
increased network management options
reduced costs*
increased flexibility*
increased bandwidth availability
decreased number of critical points of failure
2
A network engineer is reviewing a network design that uses a fixed configuration enterprise router that supports both LAN and WAN connections. However, the engineer realizes that the router does not have enough interfaces to support growth and network expansion. Which type of device should be used as a replacement?
A network engineer is reviewing a network design that uses a fixed configuration enterprise router that supports both LAN and WAN connections. However, the engineer realizes that the router does not have enough interfaces to support growth and network expansion. Which type of device should be used as a replacement?
a PoE device
another fixed configuration router
a modular router*
a Layer 3 switch
3
What are two functions of a router? (Choose two.)
What are two functions of a router? (Choose two.)
It controls the flow of data via the use of Layer 2 addresses.
It increases the size of the broadcast domain.
It manages the VLAN database.
It determines the best path to send packets.*
It connects multiple IP networks.*
4
Which design feature will limit the size of a failure domain in an enterprise network?
Which design feature will limit the size of a failure domain in an enterprise network?
the purchase of enterprise equipment that is designed for large traffic volume
the installation of redundant power supplies
the use of the building switch block approach*
the use of a collapsed core design
5
How can an enterprise network be designed to optimize bandwidth?
How can an enterprise network be designed to optimize bandwidth?
by installing devices with failover capabilities
by deploying a collapsed core model
by organizing the network to control traffic patterns*
by limiting the size of failure domains
6
As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
As the network administrator you have been asked to implement EtherChannel on the corporate network. What does this configuration consist of?
grouping multiple physical ports to increase bandwidth between two switches*
providing redundant links that dynamically block or forward traffic
grouping two devices to share a virtual IP address
providing redundant devices to allow traffic to flow in the event of device failure
7
Which technology is required when switched networks are designed to include redundant links?
Which technology is required when switched networks are designed to include redundant links?
Spanning Tree Protocol*
virtual LANs
link aggregation
virtual private networks
8
Which statement describes a characteristic of Cisco Catalyst 2960 switches?
Which statement describes a characteristic of Cisco Catalyst 2960 switches?
New Cisco Catalyst 2960-C switches support PoE pass-through.*
They are best used as distribution layer switches.
They do not support an active switched virtual interface (SVI) with IOS versions prior to 15.x.
They are modular switches.
9
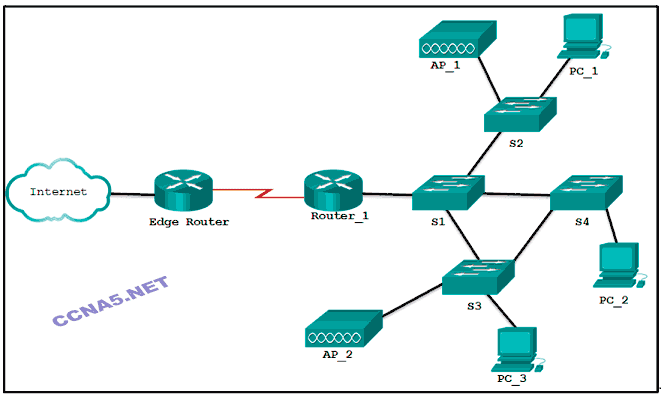
Refer to the exhibit. Which devices exist in the failure domain when switch S3 loses power?
PC_3 and PC_2
AP_2 and AP_1
S4 and PC_2
PC_3 and AP_2*
S1 and S4
10
Immediately after a router completes its boot sequence, the network administrator wants to check the routers configuration. From privileged EXEC mode, which of the following commands can the administrator use for this purpose? (Choose two.)
Immediately after a router completes its boot sequence, the network administrator wants to check the routers configuration. From privileged EXEC mode, which of the following commands can the administrator use for this purpose? (Choose two.)
show flash
show startup-config*
show NVRAM
show version
show running-config*
11
A network administrator is planning redundant devices and cabling in a switched network to support high availability. Which benefit will implementing the Spanning Tree Protocol provide to this design?
A network administrator is planning redundant devices and cabling in a switched network to support high availability. Which benefit will implementing the Spanning Tree Protocol provide to this design?
Redundant paths can be available without causing logical Layer 2 loops.*
Multiple physical interfaces can be combined into a single EtherChannel interface.
Faster convergence is available for advanced routing protocols.
Network access can be expanded to support both wired and wireless devices.
12
Which two requirements must always be met to use in-band management to configure a network device? (Choose two.)
Which two requirements must always be met to use in-band management to configure a network device? (Choose two.)
at least one network interface that is connected and operational*
a terminal emulation client
a direct connection to the console port
a direct connection to the auxiliary port
Telnet, SSH, or HTTP access to the device*
13
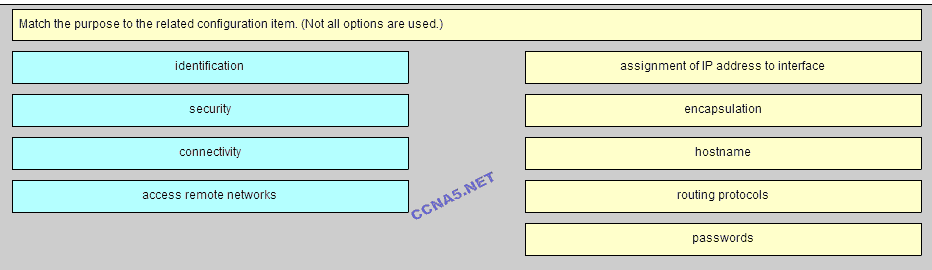
Place the options in the following order:
connectivity
- not scored -
identification
access remote networks
security
14
In which situation would a network administrator install a Cisco Nexus Series or Cisco Catalyst 6500 Series switch to promote infrastructure scalability?
In which situation would a network administrator install a Cisco Nexus Series or Cisco Catalyst 6500 Series switch to promote infrastructure scalability?
on a service provider network to promote integrated security, and simplified management
on a data center network to provide expansion and transport flexibility*
to enable virtual stacking of switches to provide cloud-managed access
on a campus LAN network as access layer switches
15
Which statement describes a characteristic of Cisco Meraki switches?
Which statement describes a characteristic of Cisco Meraki switches?
They are service provider switches that aggregate traffic at the edge of the network.
They are cloud-managed access switches that enable virtual stacking of switches.*
They are campus LAN switches that perform the same functions as Cisco 2960 switches.
They promote infrastructure scalability, operational continuity, and transport flexibility.
16
Why would a network administrator issue the show cdp neigbors command on a router?
16
Why would a network administrator issue the show cdp neigbors command on a router?
to display router ID and other information about OSPF neighbors
to display device ID and other information about directly connected Cisco devices*
to display routing table and other information about directly connected Cisco devices
to display line status and other information about directly connected Cisco devices
17
What is a characteristic of in-band device management?
17
What is a characteristic of in-band device management?
It is used to monitor and make configuration changes to a network device over a network connection.*
It uses a direct connection to a console or AUX port.
It is used for initial configuration or when a network connection is unavailable.
It uses a terminal emulation client.
18
Which two features of enterprise class equipment assists an enterprise network in maintaining 99.999 percent up-time? (Choose two.)
Which two features of enterprise class equipment assists an enterprise network in maintaining 99.999 percent up-time? (Choose two.)
failure domains
services module
collapsed core
redundant power supplies*
failover capabilities*